Challenge
WordPress site security requires constant vigilance, but manually monitoring file changes across installations is time-consuming and prone to errors. Unauthorized modifications – whether from compromised plugins, malicious access, or accidental changes – can go undetected until they cause visible damage.
Without continuous monitoring, the gap between a security breach and its discovery can stretch from days to weeks, increasing the potential for data loss, reputational harm, and costly remediation.
Solution
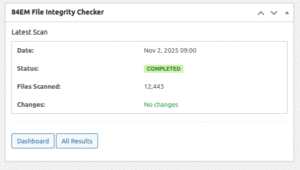
84EM developed an automated security monitoring system that continuously verifies every file in a WordPress installation against a known-good baseline. The system runs scheduled scans in the background, detects unauthorized changes, and delivers immediate notifications when modifications occur.
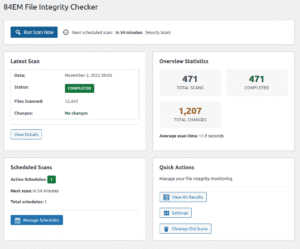
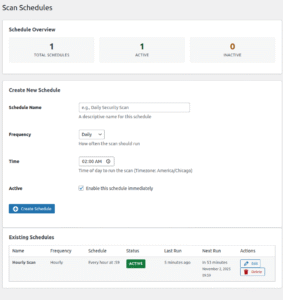
Multiple scan schedules run independently with customizable frequency and timing, and the system handles large installations without affecting site performance. Administrators set the monitoring scope once and the system operates on its own from that point forward.
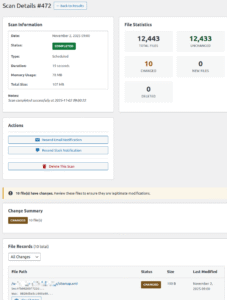
When changes are detected, the system provides a clear breakdown of what was modified, so the security team can quickly determine whether a change is legitimate or requires investigation.
Key Capabilities
- Automated background scanning with configurable frequency that tracks additions, modifications, and deletions across the entire WordPress installation, flagging any file that differs from the verified baseline.
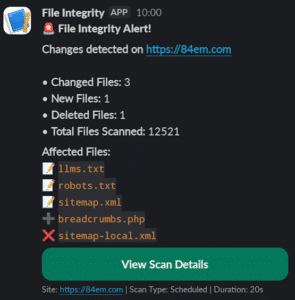
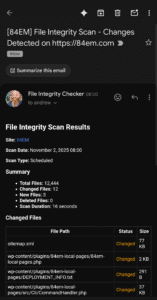
- Instant notification alerts via email and Slack when unauthorized modifications are detected, with detailed change reports identifying exactly which files were affected.
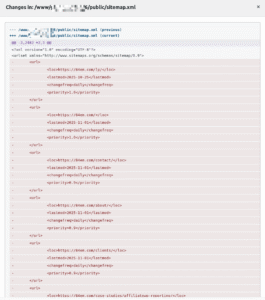
- Visual change tracking with a built-in comparison tool that displays exactly what changed between scans, with protections that prevent viewing of sensitive configuration files.
- Flexible configuration with customizable scan scope, exclusion rules, and notification preferences that adapt to any WordPress installation.
Results
Site administrators moved from manual, periodic file checks to continuous automated monitoring that runs without intervention. Unauthorized modifications that previously might go undetected for days or weeks are now surfaced within hours through automatic alerts.
The immediate notification system via Slack and email enables rapid response to potential security incidents. Administrators receive detailed change reports the moment modifications are detected, rather than discovering issues after they’ve caused visible problems.
The built-in comparison tool gave security teams the ability to assess the severity of changes quickly without manually reviewing file versions. Each detected modification includes a clear breakdown of exactly what changed, so the team can immediately determine whether a change is legitimate or suspicious.
Development teams deploy with confidence that any unauthorized modifications will be detected and reported immediately. The automated monitoring serves as a continuous security layer that operates independently of other security measures.
View the 84EM File Integrity Checker repository on GitHub
Screenshots